
This guide will demonstrate how to enable the BitLocker startup PIN for pre-boot authentication on Windows 10 with Microsoft Intune. I will walk through how to accomplish this in a nearly fully automatic way. Let’s start with some facts around BitLocker to understand the technology more precisely. In fact, I think a pre-boot startup PIN is not always necessary. To explain my point of view a bit further, we need to have a more detailed look at the encryption key material handling of BitLocker. The key material security is based mainly on the trusted computing platform concepts. Easy speaking this is the protection of the key material with a TPM (aka TPM only scenario) or with a TPM and pre-boot authentication startup PIN (aka TPM+PIN scenario).
How does BitLocker key protection work?
First, we need to understand the general procedure of how BitLocker will get access to the encryption key. The Trusted Computing Group introduced the trusted computing platform. In short, this board defined measures for trusted computing. From interest here is the Endorsement Key and the Sealed Storage concept. The underlying idea is to bind private information to the platform configuration to generate the Sealed Storage. The platform configuration includes hardware and software which is being used. The concept of the endorsement key is simple. It is a generated key during manufacturing time on a chip. The key cannot be changed and will never leave the chip. In general, both these concepts are widely known by people in the form of the Trusted Platform Module (TPM). The TPM has an endorsement key and can only be accessed from unmodified and untampered hardware and software configuration.
In a widely used standard configuration of Microsoft Windows 10, BitLocker is used with a TPM only key protection to protect BitLocker key material. As already explained Windows uses so called platform configuration registers (PCRs) to measure the state of hardware and software configuration (compare article TPM platform validation profile) and releases the key material in an unmodified and untampered configuration is available. We can easily say the integrity of the configuration is proven and therefore the key material is released for BitLocker decryption usage. This leads to a situation, that an attacker needs the complete hardware and can’t modify the platform configuration otherwise the key material is not released. Even in case the complete hardware is stolen, the device might reach the platform configuration state to boot up, but only until the normal Windows logon. At this point in time the attacker needs to overcome the Windows logon which is protected from brute force attacks by slowing down logons retries, in case of unsuccessful logons. In fact, this is a pretty safe configuration to run Windows 10 with BitLocker protection.
No downside at all?
Not really, there are always bypasses in various IT systems and this is true for this BitLocker configuration as well. The fact, that in case of an unmodified platform configuration, the key material is released and put into memory for cryptographic operations can be used for various attacks.
Attacks by accessing the memory in various ways can finally give you access to the BitLocker key material. For example, Direct Memory Access (DMA) ports and Plug and Play mechanisms are used to gain access to memory during Windows run time (aka side channel attacks). But also, the fact that cooled down transistors are not losing their programmatic state immediately, can give the attacker enough time to dump the memory and get BitLocker key material. The latest attack was done by using electric engineering tools like oscilloscope and logic analyzers to read the signals directly from the wires/bus (aka TPM sniffing). For interested readers I recommend reading – Extracting BitLocker Keys from a TPM.
Do I need to worry now?
I don’t think so! Security is always a cat and mouse game, attackers getting better and defenders build better protections. Attacks against BitLocker key material and the platform exist, and new ones will likely be found in future. In the meantime, you must think about who you want to protect your data against. If you target nation state hackers, I don’t think that all this is enough as data will be exfiltrated in some way anyway. If they can’t easily target your device, they will have a complete suite case full of options to accomplish their goals and finally get your data.
Security is about building defense lines and this involves different areas and different technology to finally operate a secure enough but still usable system. I will explain this by using an example. We can choose our hardware wisely to eliminate some side channel attacks in advance. In fact, the Windows 10 hardware certification program makes sure some of these attacks are eliminated by the design of modern hardware. Second, we build several layers of protection around our data. This includes full disk encryption (FDE), state of the art security configurations in Windows, anti-malware protections which can respond immediately in case of threats and malicious behavior, and entity security by encrypting important data individually. The overall security posture of your device (and of course the used services, but these are not in scope of this article) define a successful defense strategy. A well-designed workplace solution and the services around it, with the right principles, will give the average and skilled attacker a hard time as the defense layers are able to counter in all stages of an attack.
Additional countermeasures?
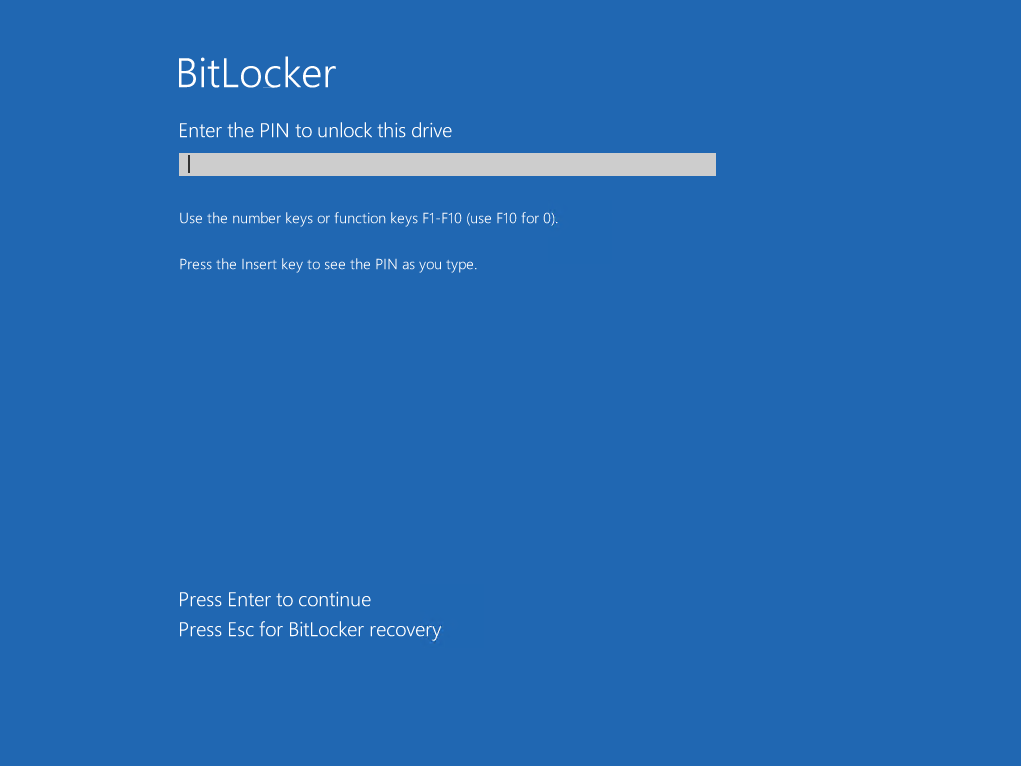
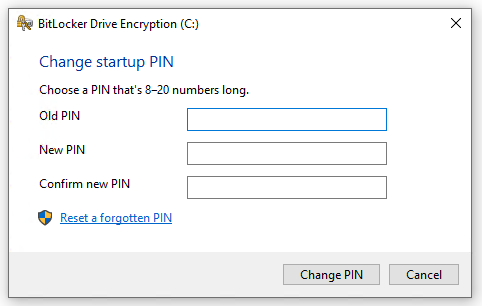
The BitLocker standard configuration in combination with other security measures will balance convenience in usability and security (please also read the Microsoft article BitLocker Countermeasures). If you think your protection level is not enough and a good overall solution can’t be accomplished in your setup, and you want to bolster your security by introducing pre-boot authentication with an additional PIN, the following guide is right for you. The additional PIN requirement during startup adds a kind of control gate to the TPM operation. The new procedure with a startup PIN is as follows. The TPM will not release any key material since the platform integrity is verified and in addition the startup PIN must be entered. Without successful PIN entry during early startup phase, the TPM will not release the key material and therefore no key material will be loaded into memory, which renders most cold boot attacks useless. This is an example of how a BitLocker pre-boot authentication startup PIN looks like:
Challenges while enabling TPM+PIN with Microsoft Intune on Windows 10
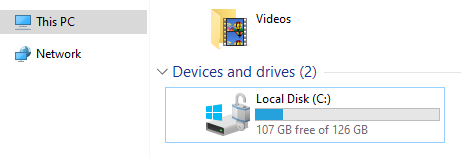
In my guide Enabling BitLocker on non-HSTI devices with Intune I’m essentially describing how to implement BitLocker encryption on Windows 10 devices with Microsoft Intune for all your devices, even the ones not holding special hardware certifications (HSTI). The guide shows the Microsoft Intune configuration profiles and how to achieve this in a automatic and silent way. The result is an encrypted OS disk without any interaction with the user.
And here lies exactly the challenge when we talk about a user definable PIN. Sure, we could fall back to the Intune capabilities to trigger the BitLocker encryption wizard and not silently encrypt the OS disk. To say it in different words, enabling silent BitLocker encryption will only work with TPM only and not if you enforce a PIN. As soon as you require a PIN you must rely on the BitLocker encryption wizard and the user you must click through it.
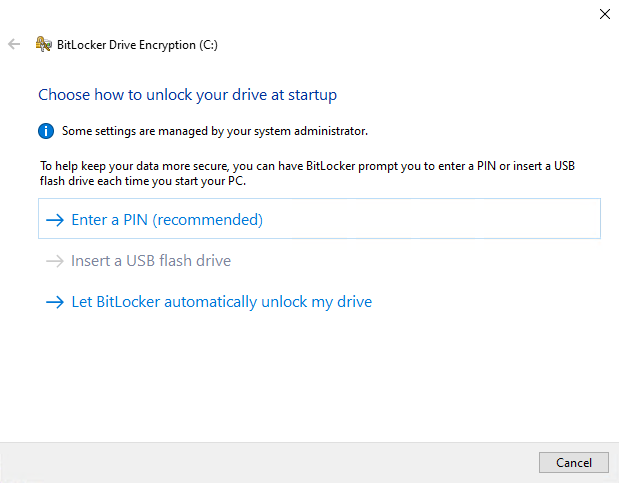
The next challenge is that we have to provide a way to do all this as a standard user. Standard user permissions are common and a good security practice. The manual way of enabling BitLocker needs administrative permissions, can be seen on the small UAC shield icon in front of the links:
The solution?
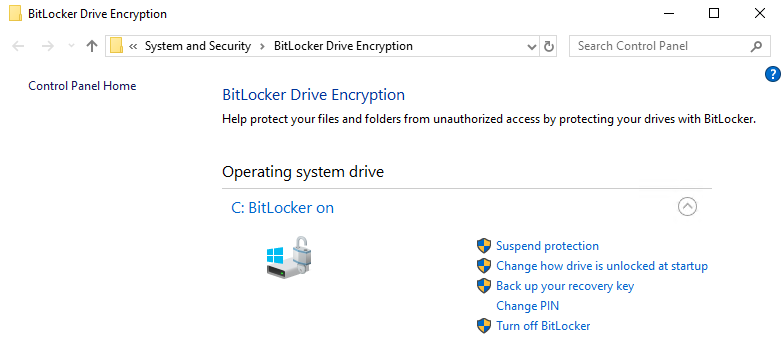
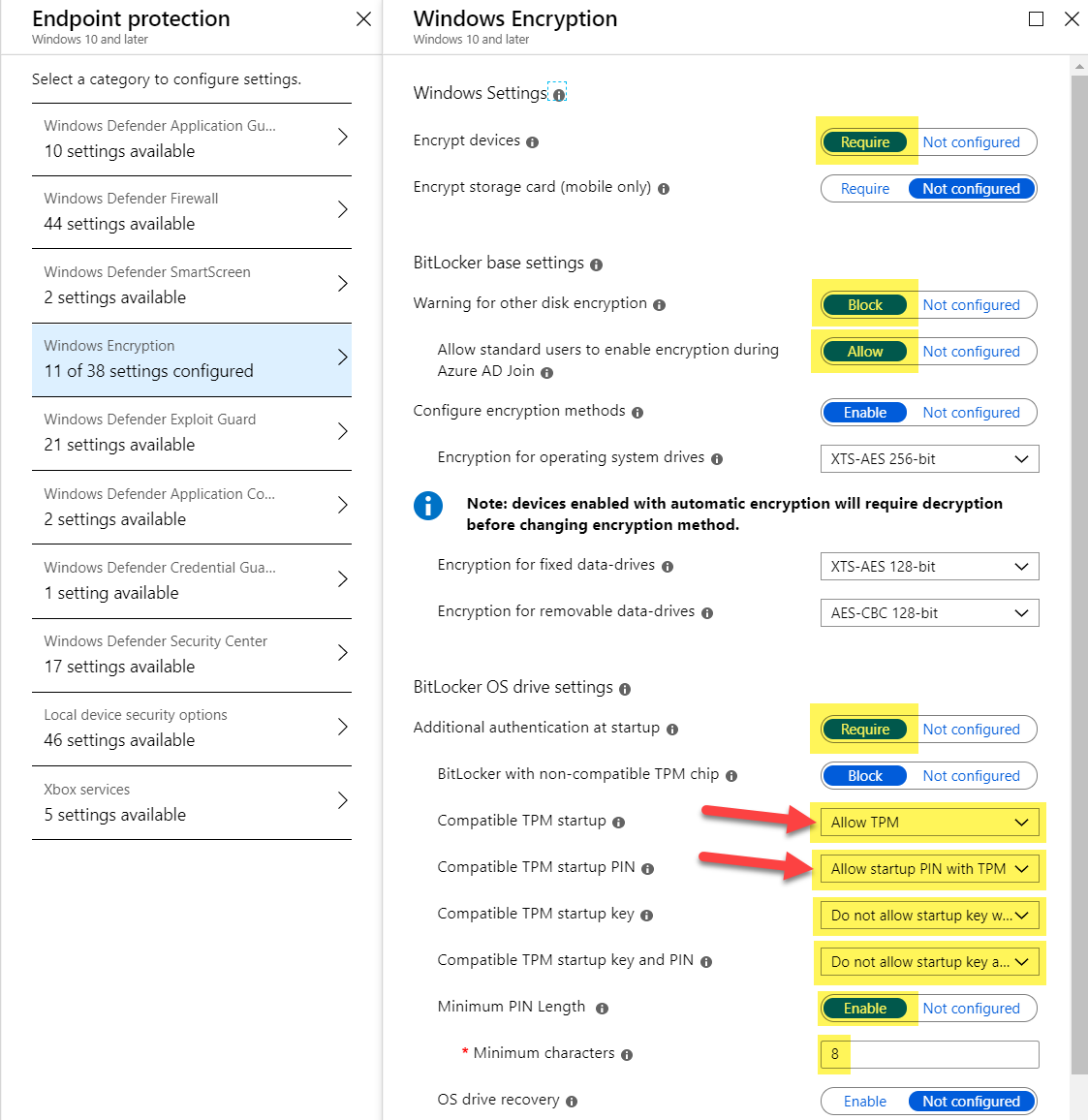
We need a way to ask the user for the PIN and encrypt the OS disk as soon as possible. The idea is to silently encrypt the disk and ask for the PIN later in the process. This way we would have a secured device right after deployment and the user must set his individual PIN afterwards. I follow the same configuration as in my last BitLocker article Enabling BitLocker on non-HSTI devices with Intune and allow “additional authentication at startup” > Allow TPM and Allow startup PIN with TPM. It is not needed to configure the “OS drive Recovery” options as the silent encryption will always backup the key to AAD. The settings below are enough to have everything in place what’s needed:
The challenge with this approach is, that we have to ask for the PIN in user context with standard user permissions and the TPM+PIN key protector must be set in system context.
I’ve created an Intune Windows app (Win32) which has a PowerShell script logic to display a PIN entry dialog and to set the BitLocker key protector TPM+PIN.
SetBitLockerPin – Intune Win32 app files
https://github.com/okieselbach/Intune/tree/master/Win32/SetBitLockerPin
The .intunewin package SetBitLockerPin can be created easily with the Intune Content Preparation Tool and the following command:
.\IntuneWinAppUtil -c .\SetBitLockerPin -s SetBitLockerPin.ps1 -o .\ -q
This way we can target the app as available to the device or user and the user is able to set the PIN as a standard user. We target the Windows app in system context for install. To escape from the system context, I utilize the ServiceUI.exe from the Microsoft Deployment Toolkit (MDT) to present the PIN dialog provided by a small PowerShell script.
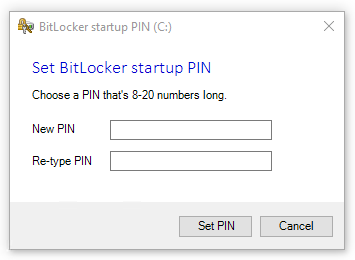
The dialog will find the configured minimum PIN length from Microsoft Intune and looks very similar to the original Microsoft Windows BitLocker change PIN dialog. I thought it helps when keeping the same style in regards of creating user adoption material later. The PIN creation dialog can be run with standard user permission as it is triggered from the Company Portal. This is how it looks like:
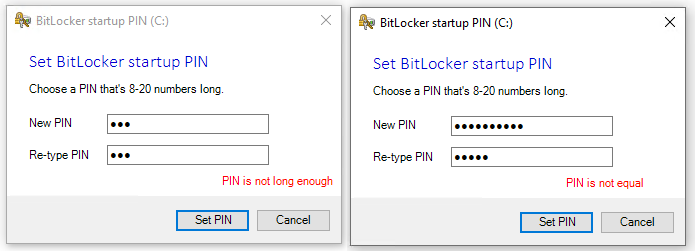
After entering the new startup PIN, the entry is passed back via a temporary file, encrypted via DPAPI to the system context. The PIN is read and decrypted by the calling script and used to configure the new TPM+PIN key protector for BitLocker. The temporary file is immediately deleted. This is an easy approach to transfer this data and the PIN itself is only short lived-in encrypted (DPAPI) in a temp file available. Basic input validation is provided like PIN length, simple PINs (1234 or 4321), and correctly re-entered PIN:
UPDATE: The dialog now even supports multi-language. There is an additional language.json file in the GitHub repo which can be used to add additional languages. The json file has sections like en-US, just copy it and change en-US for example to fr-FR and replace the English strings with French ones.
"en-US": {
"characters": "characters",
"numbers": "numbers",
"choosePin": "Choose a PIN that's {0}-20 {1} long.",
"PinIsNotEqualNotLongEnough": "PIN is not long enough",
"PinIsNotEqualOnlyNumbers": "Only numbers allowed",
"PinIsNotEqualSettingNow": "Setting valid PIN now...",
"PinIsNotEqual": "PIN is not equal",
"PinIsTooSimple": "PIN is too simple",
"BitLockerStartupPIN": "BitLocker startup PIN",
"RetypePIN": "Re-type PIN",
"NewPIN": "New PIN",
"buttonCancel": "&Cancel",
"buttonSetPin": "&Set PIN",
"labelSetBLStartupPin": "Set BitLocker startup PIN"
}
To make sure the BitLocker PIN creation dialog can only be used once I’ve created a detection logic script for the Intune Windows App (.intunewin). This small script DetectBitLockerPin.ps1 checks if the TPM+PIN protector is already set:
Write-Output $(Get-BitLockerVolume -MountPoint $env:SystemDrive).KeyProtector | Where { $_.KeyProtectorType -eq 'TpmPin' }
Use the DetectBitLockerPin.ps1 as a custom detection script in Intune and use the following command for install/uninstall (I don’t have an uninstall but it is a mandatory field)
powershell -ex bypass -file SetBitLockerPin.ps1
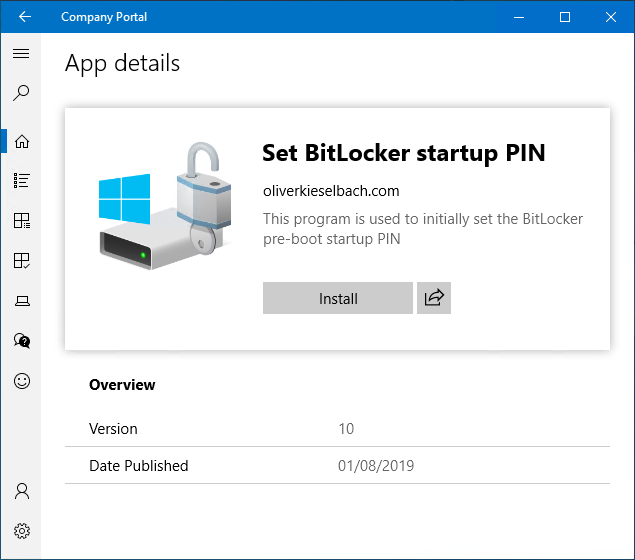
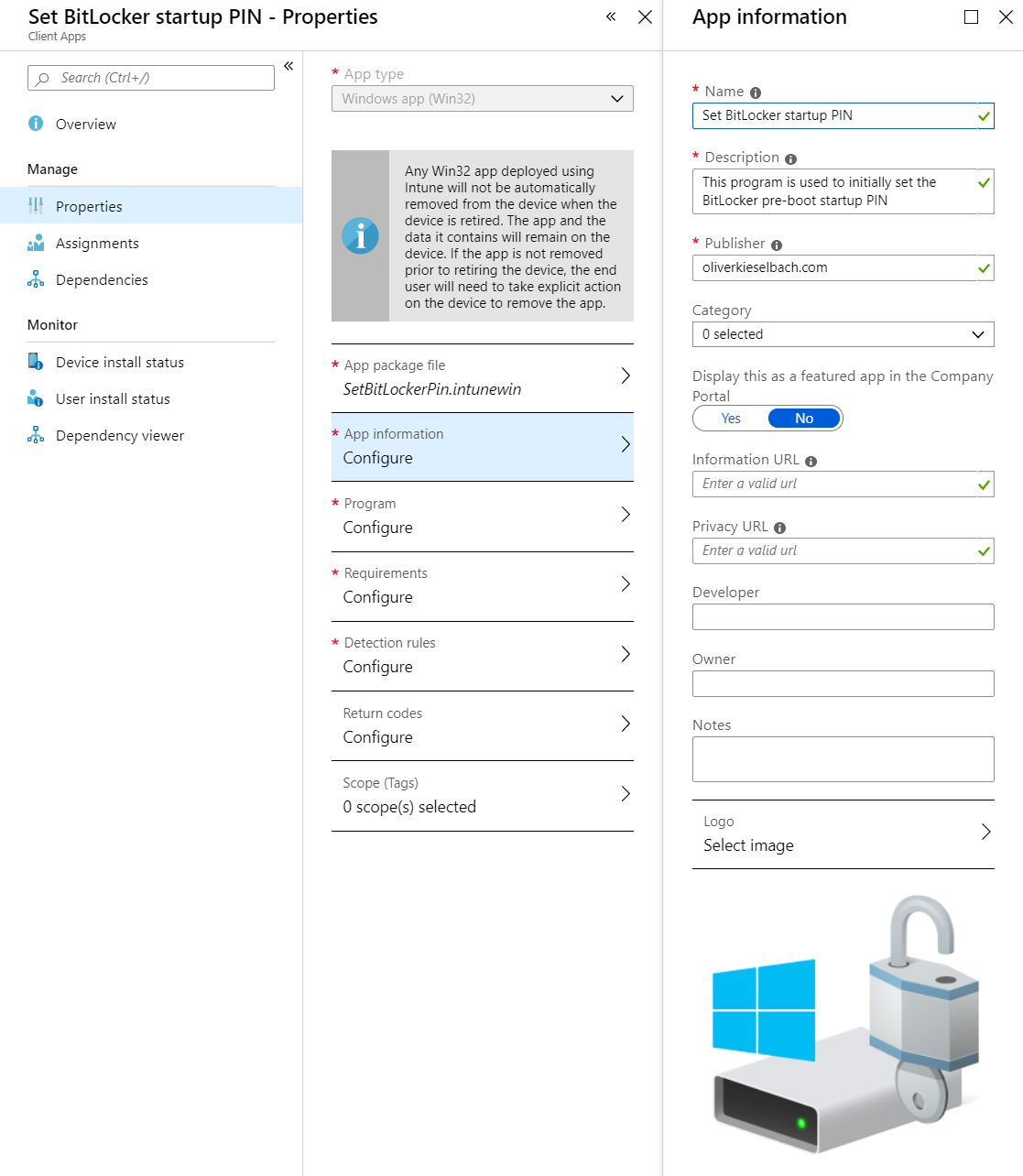
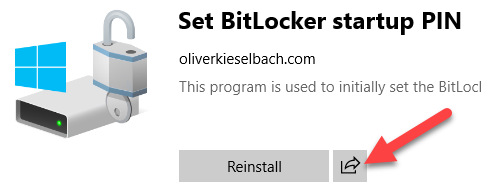
Your app Set BitLocker startup PIN app should look like this. The image is also provided in the GitHub:
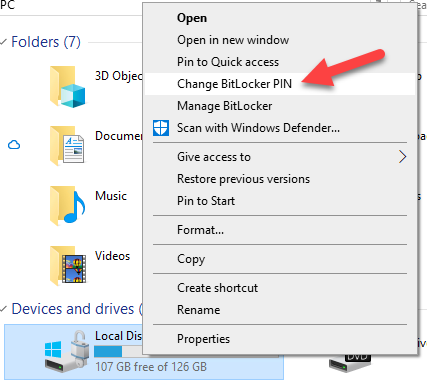
For further demonstration the very similar Windows Change BitLocker PIN dialog below. We can see it can be run without administrative permission as well:
What about reporting on the Key Protector usage?
As we have no initial PIN creation enforcement here, I thought it is good to have a way, to lead your users who need additional pre-boot authentication, to set the PIN. I’ve created a small PowerShell script which will run periodically (registers itself as scheduled task) and upload the used BitLocker key protector type information to an Azure Table Storage.
The creation of the Azure Table Storage is quite simple. For a more detailed explanation have a look at my fellow Roger Zander’s blog post BitLocker management with Azure Table Storage
The upload script for the BitLocker key protector type information
https://github.com/okieselbach/Intune/blob/master/ScheduleAndUploadBitLockerKeyProtectorType.ps1
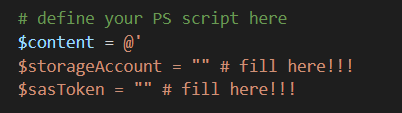
You have to fill in the Azure storage account name and the generated SAS signature for the table storage (compare Rogers post if unclear):
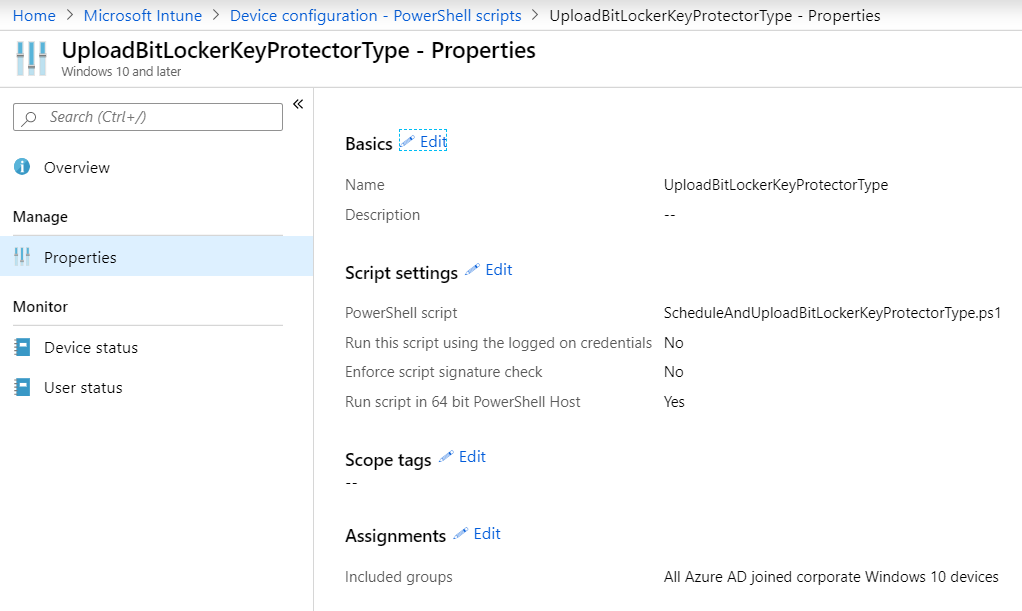
Upload it to Intune as a PowerShell script and assign it to your devices you like to protect:
The script will create a local script on the device and a scheduled task to run it periodically. Remember if you don’t like the script to run on your devices anymore, you have to create a uninstall script which deletes the script from C:\ProgramData\CustomScripts\UploadBitLockerKeyProtectorType.ps1 and the scheduled task UploadBitLockerKeyProtectorType.
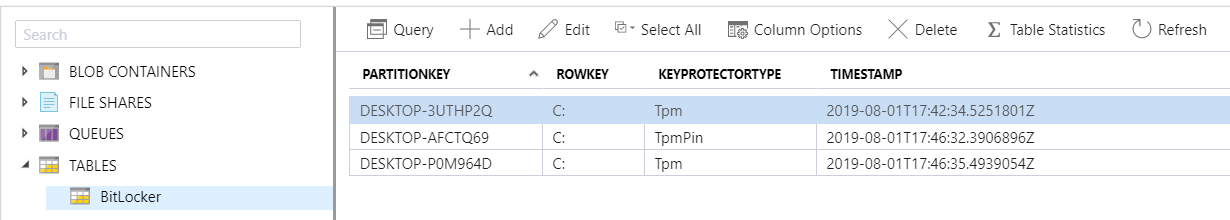
After Azure table storage creation and PowerShell script deployment, we have an easy reporting solution if the targeted device group has set the PIN accordingly to the organizational requirement.
The table storage can be viewed and queried directly in the Azure Portal:
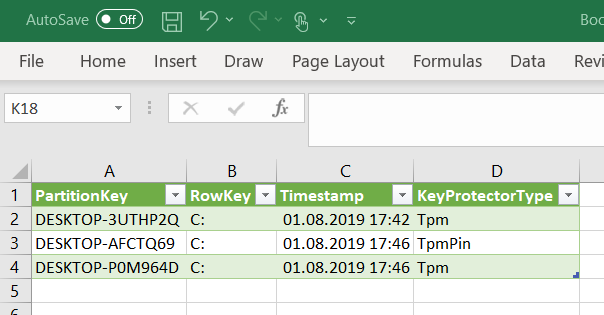
Or you connect the table storage directly with Microsoft Excel and analyze your data there:
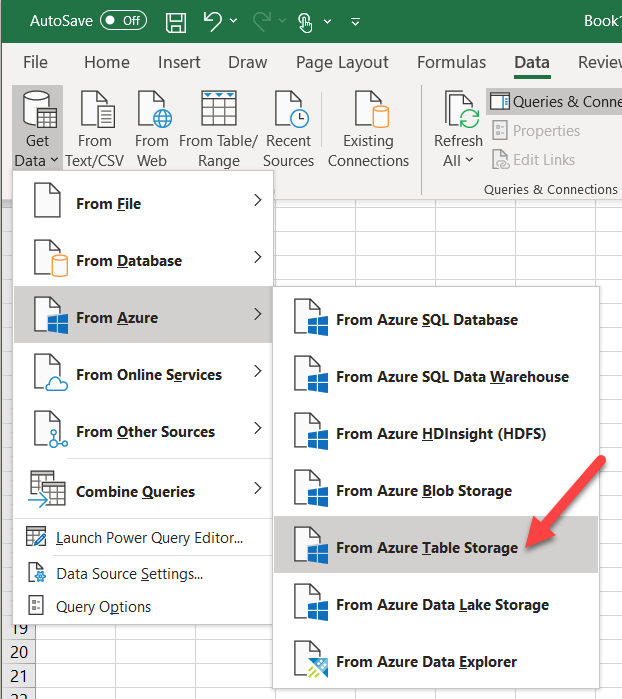
Follow the wizard and provide the Azure storage account and access key and import the table data:
What about user notifications?
To make life easier for the end users or to simply remind them to set the PIN, we can build a customized email and provide a direct link to the app in the company portal. This way the user can be targeted directly and asked to set the PIN.
First, we need to find the direct link to the app for the Company Portal. This is actually very easy but not obvious. Just use the Share button on the app in the company portal and send the information to you by email or to a OneNote:
After this you will have a link with the application guid in the form:
companyportal:ApplicationId=<yourguid>With this link you can craft an email to direct your users to the app in Company Portal. Remember this special link can only be used in an email app like Outlook who displays this as an actual link. Outlook on the web will not show it as a link:

Targeting as required app
UPDATE: 14/Oct/2022
If you like to target the solution as required app, the requirement rules can help! See my article here:
Post ESP Intune Win32 apps installations
Summary
I’ve demonstrated a way to securely deploy Windows 10 with encryption and enabled easy handling to add the PIN as additional pre-boot authentication for BitLocker. Although this is a solution to set a startup PIN with Intune, I really recommend thinking twice as a PIN might not bring additional protection if the users are bugged by yet another PIN for the system. If they set them to the same as Windows Hello for Business or even worse, they write them down on a post-it and store them along with the device you have no security improvement. This would lead to a situation where an attacker has quite an easy situation, just steal the device and use the PIN written on the post-it for pre-boot authentication startup PIN and for Windows Hello for Business. This situation would have dramatically lowered your security posture, which was surely not intended. A pre-boot startup PIN can protect but should be set on systems where users are understanding the risk and actively supporting this security measure. I think for most users, security must be relatively simple, otherwise they won’t support you or even do things which will lower your security.
Thanks for reading and always think twice about security settings and how they will bring value or maybe harm your environment.

Nice work. I will check it this week in my test tennant.
I changed some Bitlocker settings to make the “silent” encryption work.
After a few minutes, when i log on for the first time, I start the app from the Company Portal and it asks me to set the PIN.
But the Company portal says it failed (i am using the PS1 for the detection), but when i reboot it asks me but running it the 2nd time it shows a Succes message.
Btw on my first machine i recieved an error code,0x87D30065, not sure, but it was maybe related to install context (was on user changed to system).
Hard to say what is going wrong. When assigned as available and running in system context it should work, I have it running on several devices. Did you check the Intune Management Extension log files?
check here: C:\ProgramData\Microsoft\IntuneManagementExtension\Logs
What does the log file tell you?
I see error 1008 during the first detection after setting PIN and some -2016214939 (??) error messages after these lines.
After the first succesful detection everything is green again (well not red in trace32).
I will put a clean win10 again to see if this is just a one day fly error 🙂
Okay yes try it on a clean install 👍. Which Windows 10 Version are you using? I did only tests on 1809 and 1903.
I am using 1809, but all green here when run the App again on the same machine with a clean install.
I even started the app after logging on for the first time.
Hello,
I have setup the win32 app in Intune, and deployed it (required) to end users machines, but it is not getting deployed.. No error is showing up though..
What could it be..
1- I don’t have the portal installed on client devices, i am using auto enrollment
2- The app been deployed (required)
Regards,
Hi Samer,
you should have a look at C:\ProgramData\Microsoft\IntuneManagementExtension\Logs\IntuneManagementExtension.log. That’s the log file of the IME and it is quite chatty. In general you find all necessary information what is going wrong in there. Did you already checked it?
best,
Oliver
I have went through the logs and seems the installation has been successfully done.
[Win32App] Installation is done, collecting result IntuneManagementExtension 8/15/2019 10:57:22 PM 3 (0x0003)
Where i can grab the app from ?
Regards,
Hi Samer,
what do you mean by where can I grab the app from? My app is not a regular app, it is just a collection of scripts to present the dialog and configure the PIN. When you click on the app in Company Portal it will get downloaded to the temp folders of the Intune Management Extension (IME) and then after execution IME will cleanup again. Did that answer your question? The files are not installed somewhere to C:\…
best,
Oliver
Hi Oliver,
As i said, i don’t have the company portal installed on client machines.. we have been using auto enrollment.
How can i work that out in my case.
Regards,
Sasmer.
Hi,
okay auto enrollment is fine, I use it for all implementations, but you can still use the company portal. Go to the store and install it or install it directly via Intune during enrollment. In fact you have to use the company portal if you want to use Win32 app installations which are targeted as available. My solution is targeted as available otherwise the app might get installed during the Enrollment Status Page (EESP) where no user interaction is possible. That’s how I make sure the app is installed only when user interaction is possible. Therefore I let the user click it by his own and monitor the process, and send him a emails for example as remainder. If you target it as required it probably will break your enrollment procedure if you are using ESP. You maybe can think of a clever requirement rule so that the app install runs only if the users desktop is available but I didn’t researched this.
best,
Oliver
Hey Oliver,
I have spent a week trying to figure this out. This is such a goldmine getting it to work correctly.
Only issue i am having with it is during the Apps deployment stage of OOBE, the popup window is stuck behind the OOBE screen and cannot bring it to the foreground (You can see it if you alt+tab but cannot bring it to the foreground). Got any tips for this?
Regards,
Dave
Hi Dave,
this is why I made it as an available deployment in the first place. My approach was to scope this to devices where it is really necessary and people using it the right way. If you deploy it as required you will face exactly this issue. You could try to workaround with a clever requirement rule for the intunewin to prevent the install until the real desktop is shown, but you need first to find a good indicator for that. The user experience would then be, that you get the prompt right after the Desktop is shown. I’m not the biggest fan for a mass rollout of this, as normal users might not deal with the second PIN the right way. Therefore I target this only to devices which are required to have that and let the user click it as a conscious act. To drive compliance I use the table storage for reporting and send mails. If you have the requirement for all devices I would first challenge this if it not might lower the security if people are bugged by yet another pin and in the worst case write them down and store them along with their device. Anyway, if you have to solve this, have a look at the requirement rules in Intune and use a script to check if the ESP is gone or Desktop is shown (needs research). This could prevent the execution of the Win32 app until you are able to interact with the PIN dialog.
best,
Oliver
Good Morning
I was wondering how to publish your app in the Company Portal?
Grateful if you could share the steps.
Thanks a lot
Koomar
Hi,
that is actually very easy, just follow my paragraph in the article which begins with that sentence:
To make sure the BitLocker PIN creation dialog can only be used once I’ve created a detection logic script for the Intune Windows App (.intunewin).
use the information in the paragraph for detection logic, install command line and properties. Then do an assignment to your device or user group with the install type of “available”. The result is it will show up in the Company Portal after the user opens the Compand Portal. If you users don’t have the Company Portal you must tell them to download or you can assign the Company Portal to them via Intune as a required install. Again, after they have the portal opened, they will see the app. I do not recommend to deploy the app as required as the app will try to open the dialog during initial enrollment at the time of the Enrollment Status Page (ESP) and in that phase you won’t be able to interact with the dialog. That’s why I target it as available and monitor that users are actually enabling it with the azure table storage.
best,
Oliver
Hi Oliver
Thanks for your quick response
I will try and update you of the result
Koomar
Hi
This is my feedback
After I selected the app from the company portal, it took a while and never completed.
After the reboot it I got the “Setup PIN” so I thought the machine needed a reboot
So I checked the installation status in intune and I got the following:
Application Failed
Error code: 0x87D1041C
The application was not detected after installation completed successfully
I deployed the app as you recommended and did put the detection script
Can you advise?
Thanks
Koomar
Hmm okay, I never experienced this. Can you re-produce this error? Is it consistent on all your test devices? I would like to find out if it is a general problem or just this device. My tests didn’t showed this behavior.
best,
Oliver
Hi Oliver,
Just to confirm things i should be using:
powershell -ex bypass -file SetBitLockerPin.ps1
for Install & uninstall command ?
Regards,
Yes that’s correct. I use:
powershell -ex bypass -file SetBitLockerPin.ps1
the uninstall is the same as the install as I didn’t have an uninstall logic and it is a mandatory field in the portal.
best,
Oliver
Hi Oliver,
Let us supposed i got the app installed successfully, but i am not getting the BitLocker window to set the password after clicking on the app to get launched. No relevant errors showing !
Any advise please ?
Regards,
You have to check the Intune Management extension log file (C:\ProgramData\Microsoft\IntuneManagementExtension\Logs) otherwise it is really hard to tell what is going wrong in your situation.
best,
Oliver
Hi Oliver
The script doesn’t seem to run properly for a standard user. However I noticed it work for a user who is an administrator on the device
Is this required that the user is an admin on the device?
Please let me know
Thanks
Koomar
Hi Koomar,
I’ve tested it with standard user and it was working as expected, I execute the logic in system context and do the trick with ServiceUI.exe to call an UI in the user context. So standard user context is supported and that’s exactly my test scenario.
best,
Oliver
I modified the intunewin config and Powershell scripts a little bit. now i am able to push this app automatically to all devices (required install). I have created requirement rules to wait for some more reboots (app requirement rule Registry key: “Computer\HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Session Manager\Memory Management\PrefetchParameters\BootID Greather then 5” to make sure it will not be installed during ESP. Second requirement rule is nearly the same as app installation detection script. Just make sure bitlocker is already enabled. now you can push the app mandatory. I also modified the SetBitLockerPin.ps1 to set a default PIN if the user just clicks on cancel… then a default bitlocker pin will be set.
Hi wolfgang,
Can you tell me what you changed on the SetBitLockerPin.ps1 to enforce a default PIN?
Hey Courtney,
that is simple, Wolfgang modified the Cancel method to set an exit code different then 0, I changed it as an example below to 654321
$buttonCancel_Click = { $labelPINIsNotEqual.Visible = $false $textboxNewPin.Text = "" $textboxRetypedPin.Text = "" [Environment]::Exit(654321) }This way after clicking Cancel the device would get a PIN of 654321. But I’m not sure if this is a good user experience. Maybe modify the button additionally to set the name of the button to set default PIN. In my opinion a user will expect that nothing happens if he clicks Cancel and not setting a default PIN. So rename the button to something meaningful might be worth.
best,
Oliver
i did it another way. i just added some more text in the popup telling the user that it will set a default PIN if the user doesn’t enter an own pin. Then i just added another entry in “SetBitLockerPin.ps1”
.\ServiceUI.exe -process:Explorer.exe “$env:SystemRoot\System32\WindowsPowerShell\v1.0\powershell.exe” -NoProfile -WindowStyle Hidden -Ex bypass -file “$PSScriptRoot\Popup.ps1”
$PIN = $LASTEXITCODE
If ($PIN -gt 0) {
Add-BitLockerKeyProtector -MountPoint $env:SystemDrive -Pin $(ConvertTo-SecureString $PIN -AsPlainText -Force) -TpmAndPinProtector
}
else{
Add-BitLockerKeyProtector -MountPoint $env:SystemDrive -Pin $(ConvertTo-SecureString 999999 -AsPlainText -Force) -TpmAndPinProtector
}
Hey guys,
I followed what wolfgang said about adding another entry in “SetBitLockerPin.ps1” and set the app to required and the BootID to greater than 5. It appears to be working; however, I am never prompted for the PIN, it just sets it to the default PIN once the machine reaches its required number of reboots. Any ideas?
Hey Courtney,
this is hard to say without seeing the modifications you did. Did you check the Intune Management Extension log files? What are they telling?
best,
Oliver
another finding: to make it work with surface devices or other tablets you need to create a regkey: HKLM\Software\Policies\Microsoft\FVE!OSEnablePrebootInputProtectorsOnSlates=1 (DWORD).
Aktuell there isnt a CSP available to configure this setting: https://microsoftintune.uservoice.com/forums/291681-ideas/suggestions/37175833-enable-use-of-bitlocker-authentication-requiring-p
Dude thank you for that awesome additional info. For the extra script requirement for the win32 package, did your bitlocker detection look like this?
Write-Output $(Get-BitLockerVolume -MountPoint $env:SystemDrive).VolumeStatus | Where { $_.VolumeStatus -eq ‘FullyEncrypted’ }
I assume that’s the status we need to wait for, or does in progress work as well? Thanks!
Hey Jesse,
I think Wolfgang used the Intune App requirements rule with type registry check directly on the app definition in the Intune Portal and added:
“Computer\HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Session Manager\Memory Management\PrefetchParameters\BootID Greather then 5”
The Detection script is still the same: Write-Output $(Get-BitLockerVolume -MountPoint $env:SystemDrive).KeyProtector | Where { $_.KeyProtectorType -eq ‘TpmPin’ }
This makes sure the configured PIN is recognized in the end and the app is flagged as successful.
best,
Oliver
When I run this command – c:\temp>.\IntuneWinAppUtil -c .\SetBitLockerPin -s SetBitLockerPin.ps1 -o .\ -q
I get this error: The setup file you specified can not be accessed.
Can you help?
Hi Travis,
maybe you have to unblock the file. Internet downloaded files are tagged. right click on it and unblock the file and check if that helps. Otherwise I think you might have a problem with the folder path. You have to have the IntuneWinAppUtil in C:\temp in my example and a sub folder SetBitLockerPin with the SetBitLockerPin.ps1 and the other files in it. as output path If specified .\ which means in this example again C:\temp.
best,
Oliver
Hi Oliver,
I managed to get past that so thanks. But now my issue is trying to install the app–it’s failing from the Company Portal with error code: 0x80070001 (I did a Google and I think it’s this – CAUSE: Some source files were missing. The most common issue is some software has pre-requisites).
I’m wondering if I provisioned the app incorrectly. I know there’s a bit in your documentation about calling the ServiceUI.exe but I’m confused as to where this fits in – do I need to put this file in the folder where the PS script resides when first running the deployment tool?
Many thanks,
Travis
Hi Travis,
yes you have to put the ServiveUI in the same folder where the PS script is. Popup.ps1, ServiceUI.exe and SetBitLockerPin.ps1 must be in that folder. Then create the .intunewin and this should work.
best,
Oliver
Hi,
I’m getting the same issue as Travis regarding the error code: 0x8007001. I had all of the files in a folder and pointed to this folder utilizing the Win32 wrapping tool. I also included the detection script.
Hey Melissa,
this sounds good basically that’s how it is support to be wrapped. the detection script is not necessary but it doesn’t hurt there. Did you configure to run the app in System context (Install behavior = System)?
That’s the way it should work. All file in the intunewin, configured to run in system context for adding TPM PIN and ServiceUI does the trick to bring the popup to user context.
best,
Oliver
Thanks Oliver. I have this set to run in the system context. I may have downloaded the detection script in the wrong format. Can you manually set the detection rule as well?
This detection rule gathers the TPM status, this is only possible with this small PS helper script.
Hi Oliver,
So your solution has two parts? one is for encyrpting devices and second rule is for add pin? or you do this in one intune configuration profile?
Hi Rafal,
Yes, you let the device encrypt with TPM only automatically with the intune configuration profile and then later the script adds on top the BitLocker PIN.
best,
Oliver
Hi Oliver, could you tell me are you used two configuration profiles to configure bitlocker encryption with PIN?
No just one configuration profile to encrypt automatically and on top the intunewin app with the scripts to add the BitLocker PIN later.
This silent bitlocker will work on azure hybrid joined devices?
Hi Rafal,
the BitLocker CSP and silent encryption works for Azure AD joined devices only, here the docs snippet:
Starting in Windows 10, version 1803, the value 0 can only be set for Azure Active Directory joined devices. When RequireDeviceEncryption is set to 1 and AllowWarningForOtherDiskEncryption is set to 0, Windows will attempt to silently enable BitLocker.
https://docs.microsoft.com/en-us/windows/client-management/mdm/bitlocker-csp#allowwarningforotherdiskencryption
best,
Oliver
Hi Oliver,
I’ve done everything I believe correctly however the app is still failing.
I looked at the AgentExecutor logs and I get –
<![LOG[error from script =File C:\Program Files (x86)\Microsoft Intune Management
Extension\Content\DetectionScripts\3baa5edc-4b33-42b5-accf-35e24df61c11_4.ps1 cannot be loaded. The file C:\Program
Files (x86)\Microsoft Intune Management Extension\Content\DetectionScripts\3baa5edc-4b33-42b5-accf-35e24df61c11_4.ps1
is not digitally signed. You cannot run this script on the current system. For more information about running scripts
and setting execution policy, see about_Execution_Policies at https:/go.microsoft.com/fwlink/?LinkID=135170.
+ CategoryInfo : SecurityError: (:) [], ParentContainsErrorRecordException
+ FullyQualifiedErrorId : UnauthorizedAccess
I'm running the bypass command install/uninstall as you state.
Is this the Detection Script which is causing it to fail I wonder?
Thanks,
Travis
Hey Travis,
I think you have the option “Enforce script signature check and run script silently” set to Yes, this should be set to No. Otherwise you will see the error regarding digitally signed. Please try to set to no and verify.
best,
Oliver
Hi Oliver,
Thanks for that.
Now if I look at the executor, it looks to be executing the script but getting a bunch of errors:
Features <span cla …
+ ~
The '→Customer stories <span cla …
I've not made any changes to the script – just downloaded it and added to the detection bit in Intune.
Thanks,
Travis
Sorry Oliver – feel free to delete my second entry, it seems I cannot paste the script.
I’ve uploaded the error: http://s000.tinyupload.com/download.php?file_id=09466429946862267039&t=0946642994686226703986077
I think your detection script has content in a wrong format. It seems to have Html tags inside, this happens when the file is downloaded in the wrong way. To make sure you only get the plain text try using the Raw button to display just the plain text and copy it into a .ps1 file. This should definitely work.
Hi Oliver,
Indeed all my scripts were like that so thanks for pointing out. I thought I would get it right was saving all scripts in RAW format.
The latest error I have is: The application was not detected after installation completed successfully (0x87D1041C)
I’m trying to figure out what this means.
I know that silent encryption has taken place successfully, I just can’t for the life of me get the PIN prompt to work.
Maybe I need to provision a fresh system as running older versions of the app has made it not work in some way.
Travis.
Hi Oliver,
I managed to get it to work in the end.
I ran your script via ISE and I got an error: Program ‘ServiceUI.exe’ failed to run: The specified executable is not a valid application for this OS platform.
So I downloaded the deployment kit and copied the ServiceUI file from C:\Program Files\Microsoft Deployment Toolkit\Templates\Distribution\Tools\x64
This seemed to work for me.
Hi Oliver do you know the way to automatic enrypt hybrid azure joined device and setup later PIN >?
Hi Rafal,
a hybrid azure ad joined device is basically a domain joined device with the additional registration in AAD. Therefore hte hybrid aad join scenario aligns to the classic domain tools like MBAM for BitLocker management (on-premises management). Later we will have a ConfigMgr integration as well. Here a good article about the options: https://techcommunity.microsoft.com/t5/Enterprise-Mobility-Security/Microsoft-expands-BitLocker-management-capabilities-for-the/ba-p/544329
best,
Oliver
Hi Olivier,
First of all, thanks for sharing. This is awesome!
Secondly, I’ve noticed that if minimum pin is 6 digits and you enter a 6-digit pin that starts with any 0, then it will not meet the minimum requirement since it will only register 5 digits. And then the app will fail without any explanation.
And if the pin starts with 00, then only 4 digits is registered and so on…
I guess an alternative is to edit the text to warn users not to enter a pin that starts with 0, but unfortunately that still wouldn’t prevent the user from actually doing it.
Just wanted to give you a feedback, and if you ever make any adjustments to your great script, then let us know 🙂
Oh that’s true I didn’t thought of that during my test cases and used only PINs starting with something different then 0 :-).
You are totally right. The problem is that I thought using the return key is a quick method to transfer back the info to the System context, but this will not allow leading zeros… Hmmm… I really should enhance the .ps1 script to prevent leading zeros. Thanks for making me aware! I’m going to fix this by modifying the .ps1 and maybe think of a differnt way to pass back the PIN to the system context to support even leading 0’s….
best,
Oliver
I’ve uploaded a new Popup.ps1 with a check to prevent entering PIN’s with leading 0’s. Again thanks for making me aware!
Hello Oliver,
Would this work on Non TPM Laptops also?
Thanks,
Jon
Hi Jon,
Unfortunately not, the PIN is a pre-boot authentication (startup) feature bound to the TPM. You configure the TPM to provide access only when someone enters the PIN during startup.
Best,
Oliver
Hi Oliver, when user without admin rights try run application to setup PIN, powershell starts with error and pin was not setup, when i added admin rights to user pin working correctly? Could you tell me if your application is working correctlly? or i something doing wrong?
Thanks for answer.
Hi Rafal,
then something went wrong. That’s actually the purpose of my implementation. The standard user should be able to set a PIN with Intune. Do you have the ServiceUI.exe in the .intunewin file and what is the exact error you get?
best,
Oliver
Hi Oliver,
Could you tell me if this settings are ok?
[cid:image001.png@01D5A46E.16D3BA30]
Or here should be âinstall behaviorâ system ?
Hi Oliver I solved my problem 😊
Hi oliver,
The implementation works for me correctly on the deployed computers. But now if a user does not remember the PIN, is it possible to reset the PIN with the same method? When I return to change the PIN, the new PIN is not saved and the old one is kept. What would be the method to reset the PIN?
Thank you.
Hi David,
I’ve uploaded an additional package with a basic PowerShell Script to remove the TPM PIN. When a user uses this package to remove the TPM PIN he can set it afterwards with the SetBitLockerPin package again. This works as the detection method is not fulfilled for the SetBitLockerPin package and the reinstall will work. If the PIN is not removed the Detection method for SetBitLockerPin will detect a TpmPin and the the SetBitLockerPin package is flagged as installed instantly but the powershell script is not really executed, just the detection script. For the removal script see here: https://github.com/okieselbach/Intune/tree/master/Win32/RemoveBitLockerPin
Create a basic Win32 (.intunewin) package with a PowerShell removal script and detection method script. Execution context must be system. This way the user is able to run a removal of the TPM PIN as standard user. This is more a short hackathon of an implementation. Created it in just a few minutes. I can think of problems with the implementation and I didn’t do extensive testing. One problem I can think of is, that the package might occur as failed when the SetPin package has run. All this needs some testing and fine tuning I guess, but it gives you a starting point.
best,
Oliver
Thanks for your quick response.
I will try the solution.
Regards.
Hi,
You were right, when you run the new PIN remove script, the SetPIN gives an error in the installation message.
And vice versa when you run the SetPin script again, the removePIN script remains as a failed installation.
I cannot establish the detection methods so that the two applications are without errors.
Hmmm okay then my thought were right. I would follow the following idea… you could design a scheduled task which has the remove PIN script behind which can be triggered by a standard user. The script must be located at a file system path where standard users are not allowed to write (otherwise you will introduce a security hole). Then you could additionally build a shortcut in the start menu or desktop to easily trigger the scheduled task, which then runs in system context and is able to remove the pin. All this could be scripted and installed via a mandatory package from Intune.
Hello
I need your assistance as I have a failure as well.
Everything seems to work well.
1. Device is encrypted by Intune Config Profile during AutoPilot
2. App is deployed as required to Device
3. Pin is entered and dialogue goes away but I don’t think it is setting the new protectors TPMPin
The logs tell me Exitcode is defined as success but it actually failed according to detection result.
When I check using managed-bde -status I do not see the new keyprotectortype TPMPin and this is why I believe detection is failing.
Any thoughts?
Thanks
Chris
Hey Chris,
the script should actually gather the PIN and then set it in system context. Hard to tell what is going wrong for you. My general troubleshooting approach would be to start a command line in system context via psexec -i -s cmd and then run the scripts from there to see what happens. In case needed I would add some debug output to narrow down the issue. Something might get wrong during PIN handover to system context and then the script does not successfully set the PIN but also there might be an issue to send a proper error message during this…
best,
Oliver
Hi Oliver thanks for getting back to me. Turns out it was a problem because I was testing on a surface pro4 and for slates and tablets I had to add a registry key for “EnablePreBootInputProtectors” after this everything worked really well. Worth noting is that when testing on 1809 the prompt for pin came up during AutoPilot ESP and 1903 it somehow waited until after AutoPilot which is actually preferable.
Many thanks though really useful scripts, although actually after some thought I also agree that TPM Pin when using Hello for Business is likely to end up in similar Pins being used so I may not implement Pin after all, but at least its good to know it works if needed and best of all its possible without re-encryption.
Hey Oliver,
Could you explain something for me – What exactly does “Allow TPM” setting do? Once we set that to “Allow TPM” – we receive a GP error when trying to enable bitlocker pin through a script that gets dropped via Intune. Once we switch it back to “Do not allow TPM” the error goes away.
Hi Nik,
Allow TPM basically means to allow the usage of the TPM. It is not enforced but allowed. In your case this should not block you from using a PIN. For the TPM+PIN usage you need additionally allow TPM + PIN setting. You wrote GP so I guess you are using Group Policy and Intune make sure you are not running into a conflict when using MDM and GPO settings. Hope it helps a bit.
best,
Oliver
I’m loving this, thank you so much…. UK Gov highly recommends using TPM+PIN, so that left me in a pickle with Autopilot, which this looks to really help with. I might also create a UserVoice if one doesn’t exist for OOBE to look for the policy just after initial signin, and allow some interaction with user to ask for a PIN or some such, doesn’t seem too difficult a thing to request.
My plan for the last part, the email… I’ve added an extra column in the table called ContactAttempts, then I plan on creating a Logic App that runs on a schedule looking for anything that’s TPM only, and then email the staff and increment the counter… give them something like 4 attempts and then block them. Or in reality message into their Teams as well as an email, and if increment goes to high then look up their manager and include them. Or some such.
Can this solution be implemented in a domain without Intune?
Hey Tom,
in a Domain without Intune you should have a look at the MBAM feature of ConfigMgr. This provides all the features you like to have. My solution is actually built in the context when using Intune to have an equivalent solution like MBAM in ConfigMgr. But, you could use the script and package it with a different Software distribution solution and use it. It would need GPOs to set TPM only and my solution packaged with a different Software Distribution and then deployed via a AppStore/SoftwareCenter whatever. So, in theory it should work also with Domain and different Software Distribution system.
best,
Oliver
Hi Oliver,
During our testing, we noticed that if the computer restarts during the Bitlocker Pin prompt, even without any input in the textbox, Bitlocker will ask for the PIN. In this case, user will not know what is the PIN because it was never set before. How can we prevent this issue?
Hey Johan
Oh, I think this is because the PIN handover is done after Window Close. As soon as the device reboots I think it will receive a Window close and the popup will be closed without writing the PIN as there was no input. The underlying script picked it up and set the PIN protector but I guess the file was empty then and it wrote an empty PIN. Actually I thought it should even not create txt file and then don’t do anything. But anyway I added an additional content check to prevent setting a PIN if no valid content was found. It fixed the behavior you described. So, please test again with the latest version. This resolved the issue in my test environment.
best,
Oliver
Hi Oliver,
Tested on my lab and it is working as expected. Thanks a lot!
Thanks for this, this is great.
How would you configure this to allow for an Alphanumeric pin to be set?
Actually I never tested the solution for Alphanumeric. I think the complexity must be read from registry to alter the behavior from the popup to support Alphanumeric during input validation and the rest should work. A bit of PowerShell code to add and this will work also I think. I will give it a try as soon as I have some time.
Hey Oliver
I’ve integrated this into AutoPilot but I’ve noticed something that makes no sense (to me at least)
So if the Profile is for a Hybrid Domain Join machine, I get the screen pop for setting the PIN (ServiceUI.exe) during the App Deployment portion of the process. If I switch the profile to Azure AD Join only, the ServiceUI.exe process isn’t given focus so I need to ALT-TAB and I can enter the PIN blindly as the process is never overlayed – hopefully, I’ve explained this behaviour well enough 😀
Thanks
Hi,
I actually did not recommend to assign it as required because of unforeseeable reasons like this. In the comment section there are hints from other readers how a detection logic can be implemented to delay the execution of the package until the desktop is shown. Why this issue appears only on AADJ is unclear to me. I would suggest to play around with the Detection logic to delay the execution.
best,
Oliver
Don’t know if it’ll help anyone, but I hit some issues with Surface devices… they need a particular registry key, which you can’t deploy with Intune (no CSP).
I’ve edited SetBitLockerPin.ps1 to include:
$pcModel = (Get-WmiObject -Class:Win32_ComputerSystem).Model
If ($pcModel -Like ‘Surface*’) { New-Item -Path HKLM:\SOFTWARE\Policies\Microsoft -Name FVE -ErrorAction SilentlyContinue; Set-ItemProperty -Path HKLM:\SOFTWARE\Policies\Microsoft\FVE -Name OSEnablePrebootInputProtectorsOnSlates -Value 1 -Type DWord -Force }
Which I think should help and do the trick.
Hello! Is it possible to enable Pre-Boot BitLocker startup PIN without this PowerShell script? In my case all my users have admin rights.
Hi Oleg,
Yes it is possible with administrative users. As soon as you require a PIN with Intune native (Require PIN setting), you must rely on the BitLocker encryption wizard and the user you must click through it. There is a screenshot in the article which shows the wizard. The user will be notified to configure it and then you are good to go. My solution is needed for standard users, as the native wizard works only with administrative users.
best,
Oliver
I spent more than 8 hours for configuring….((( , but no luck. I don’t know what I do wrong.
https://softserveinc-my.sharepoint.com/:i:/p/omelny/EShqfbs9O31FtVUYI0jCHIMBXqVSx8ZMfccGDh3AqZxhog?e=m8VJI7
Hey Oleg,
I did successful test with the native wizard by setting all TPM settings to allow and the TPM + startup PIN to required. This will enforce the startup PIN as it is required and I got the desired result. Maybe your explicit “Do not allow” setting does block the TPM + Startup PIN to kick of the wizard. Can you try to set the other TPM settings to Allow and only the PIN to require… I think that was the set I was successful with.
best,
Oliver
Nope..((( I still have a problem. So, now according to Bitlocker logs (The group policy settings for BitLocker startup options are in conflict and can’t be applied.) Could you make a screenshot and save there https://softserveinc-my.sharepoint.com/:f:/p/omelny/Ep8JdcnXIRtFsOc0zqs70VwBTCAwth__KCwg5B2K0M6YZA?e=B6C7F3
Thanks in advance!
I did a short test in my lab environment and documented it in a word doc.
Thanks for your information, but I still have an error. I click Yes for starting encryption but after that, another window appears with Device encryption (device encryption is off) . I try to turn the button (turn on) and I see the message “something went wrong. Try again later” I shared the screenshot in my share.
I’ve just found out encryption is works on my virtual machines) But don’t work on my laptop Dell Lattitude 5480. I don’t understand such behavior) You know I tried to use McAfee Antivirus with module MNE (Manage Native Encryption) which uses Bitlocker. And encryption with preboot pin works properly.
Anyway thanks a lot for your time!
Hey Oliver.
I’ve written a PowerShell toast popup that I’m going to run by scheduled task every day on LogOn which checks for TIM PIN and nags if not set.
To check for the Pin the user needs to be running PowerShell as admin, so I guess I’ll copy your example and create the scheduled task as SYSTEM… but… how to get the toast running for the user? I suppose similarly use the ServiceUI.exe as you have… but I’m a bit lost as to what the command for the scheduled task would be?
Thanks if you can help! 🙂
Cheers,
Steve
Hey Steve,
maybe you have a look at my “Install-LanguageExperiencePack.ps1” install script here: https://github.com/okieselbach/Intune/tree/master/Win32/SetLanguage-de-DE
This script is running as system and I escape via scheduled task into the user session, that is what you need and once in the user session you can kick off the toast message. Instead of ServiceUI I use a scheduled task to switch the execution context…
best,
Oliver
Thanks Oliver! Will take a look. 🙂
Wonder if we can optput a message saying PIN Set once its successfully set, or say Default Pin set to xxxxxx. I have removed the cancel button but not the cross on the right up corner. I want to force the user to set something.
Also wonder is it any better to push the mabm client to the intune device and use reg settings to get the pin set prompt. I am currently pushing the mbam client for pin reset as the inbuild bitlocker reset ask for the old pin too.
You are free to modify how you want it to be, it is just PowerShell Code so go ahead with that if you like.
I‘m not pushing MBAM as I manage modern workplaces without ConfigMgr etc. plain Intune. For me this was a good way to achieve my goal without discontinued standalone MBAM (it is part of ConfigMgr now) and I don‘t want any on-prem dependency. Simple, just the dialog and set.
Thank you, the reson i push mbam client via intune is get give the user option to reset the bitlocker password without typing the old password (unless there is anotherway around with modern management)
Did anyone get the alphanumeric PIN to work, and what changes fi you need to make to the PS1 script?
Thanks.
Hey Andy,
actually I never designed it for alphanumeric, so it will definitely not work. If I have some time I will have a look and implement some functionality to handle alphanumeric correctly.
best,
Oliver
Hi Oliver,
That’s great news. We have an imminent need for some large UK organisation who would benefit from alphanumeric pin, as it’s the default uk gov position.
Hey Andy,
I’ve checked the BitLocker PIN script for BitLocker Enhanced PIN usage now. The current script works fine and I added some additional code to tell about Enhanced PIN usage. I do this by checking if Enhanced PIN registry key is configured upfront. So give it a try. In my environment it is working flawlessly and I could add a PIN like “asdf1234$” for testing purpose.
best,
Oliver
Hey Oliver, great script!
We just tried using this for our autopilot deployments but we use the SCCM client on them as well so we couldn’t deploy the script via intune.
Had to change the Detection script to the following:
$vol = Get-BitLockerVolume
$keyprotectors = $vol.KeyProtector
if ($keyprotectors[1].KeyProtectorType -eq ‘TpmPin’)
{
Write-Output ‘TPM Pin Set’
}
The only problem is that your script allows pin codes like “123456, 654321, 111111” etc to be set.
Thanks and yes your change might be necessary as I did only test with Intune! Also yes, the complexity is not checked in the popup PowerShell script. But it is PowerShell and if you look at the $buttonSetPIN_Click definition you can easily change the code there to do whatever you like as extra checks. I think it would involve some scripting logic to do the clever checks but it can be added. So feel free to enhance the function.
best,
Oliver
Hi Oliver,
Wonderful work on that post, it helps me a lot !
But i still have some issue when i want to implement startup PIN.
I have build the .intuneapp package with ServiceUI.exe, SetBitLockerPin.ps1, Popup.ps1 and DetectBitLockerPin.ps1 files.
I create the package in Windows Apps and assign it to “Available for enrolled devices”. My test user can see the package.
Configuration profiles is ok and the system disk is encrypted.
But when the user try to launch the Set BitLocker Startup Pin from Company Portal i have an error (Error code: 0x80070001)
Maybe i miss something will creating the apps, not sure of what i must add on the Detection rules tab ?

Any advice ?
Thanks
Benoit
Hey Benoit,
sounds good in regards to the package, did you reference the DetectBitLockerPin.ps1 in the detection rules tab? Your settings regarding run as 64-bit and don’t check the signature are correct. Just select the DetectBitLockerPin.ps1 as custom detection script. That should do the trick I guess.
best,
Oliver
wonder if there is any other reg key i can put as a dependency other than the below
“Computer\HKEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Control\Session Manager\Memory Management\PrefetchParameters\BootID
wonder if there is a reg key for teams launch for first time or any other reg key/ folder available when user successfully logged on to the desktop. i had users who restarted during autopilot and the popup halt the rest of the flow and hidden behind the autopilot screen
Hey RG,
Michael Niehaus gave a tip on the other blog post about this: The simple workaround for delaying until after device ESP completes is to check if the current user is defaultUser* (typically defaultUser0, but it could be a different number in some circumstances). Maybe you try to code a small PS script to check for defaultUser*, I guess this would solve the problem.
best,
Oliver
Wonder the script works with the new bitlocker policy with the endpoint security blade. I have moved my policies from endpoint protection to endpoint security and it has stopped working. settings are identical. the manage-bde output the below
Key Protectors:
TPM
Numerical Password
Hey RG,
actually the new policy should have no impact on the TPM PIN solution. Are you sure it is related to the new policy or maybe a different error. Maybe another security setting you configured blocks now the proper execution of the PIN tool? Did you check log files of security features… I temporarily use [Environment]::GetFolderPath(“CommonDocuments”) maybe you have to change this as you do not have permission to write there anymore due to another security setting you configured?
best,
Oliver
Changing the path works, it was the defender policies. thanks Oliver
First of all, Big Thank you for your post. Finally, I’ve configured Preboot PIN with BitLocker. But, I have an issue with an upgrade from build 1903 or 1909 to 2004. I can’t do this because of preboot PIN. Feature updates 2004 failed every time. According to this article: https://docs.microsoft.com/en-us/windows/security/information-protection/bitlocker/bitlocker-upgrading-faq
No user action is required for BitLocker in order to apply updates from Microsoft, including Windows quality updates and feature updates. Users need to suspend BitLocker for Non-Microsoft software updates, such as:
Computer manufacturer firmware updates
TPM firmware updates
Non-Microsoft application updates that modify boot components
But it doesn’t work((((
I had similar situation with my onprem PCs, but we reconfigured some settings in SCCM (Suspend BitLocker PIN entry on restart)
https://docs.microsoft.com/en-us/previous-versions/system-center/system-center-2012-R2/gg682067(v=technet.10)?redirectedfrom=MSDN
(f the BitLocker PIN entry is configured on computers, this option can bypass the requirement to enter a PIN when the computer restarts after a software installation.
Always:Configuration Manager temporarily suspends BitLocker after it has installed software that requires a restart and initiated a restart of the computer. This setting applies only to computer restarts that are initiated by Configuration Manager and does not suspend the requirement to enter the BitLocker PIN when the user restarts the computer. The BitLocker PIN entry requirement is resumed after Windows startup.)
and it works properly. Do we have any option in Intune?
Hey Oleg,
interesting never heard that the PIN poses a problem. Anyway regarding your question about suspending BitLocker. No there is no equivalent in Intune, but for the upgrade process you have some hooks to run custom actions pre and post upgrade process. See here: https://docs.microsoft.com/en-us/windows-hardware/manufacture/desktop/windows-setup-enable-custom-actions
This way you could easily implement a suspend script to suspend BitLocker upfront and a enable script to enable it afterwards again.
Maybe give it a try!
best,
Oliver
Hi
i get an error on most clients “The application was not detected after installation completed succesffully (0x87d14041c)”
Hey Martin,
The detection does only look for TpmPin protector:
Write-Output $(Get-BitLockerVolume -MountPoint $env:SystemDrive).KeyProtector | Where { $_.KeyProtectorType -eq ‘TpmPin’ }
So, try to execute this by your own and see what happens. If this does not get a result your PIN is not set and you should run the SetBitLockerPin.ps1 script with psexec -sid cmd in system context and look for the detailed error message for further troubleshooting…
best,
Oliver
Hi Oliver
Can it has something to do with defender?
if i run the PS1 i get an error about ServiceUI.exe
If i try to run ServiceUI.exe manuely i can se it getting block by defender.?