Complete process automation of gathering and upload of a device Autopilot information to the Windows Autopilot service with an Azure Automation Runbook.
Read More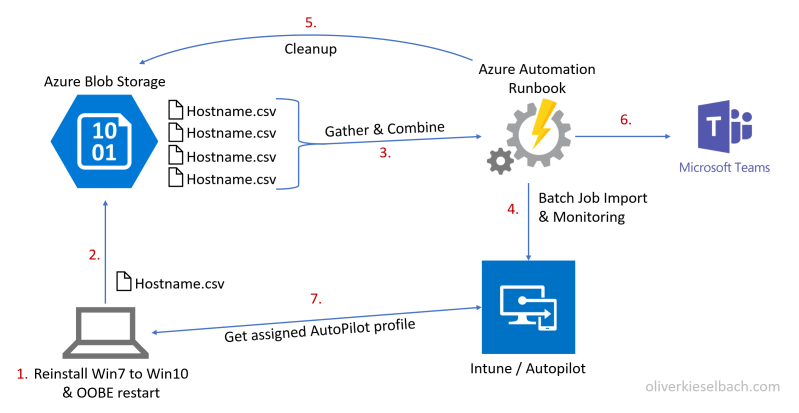
Enterprise Mobility and the Microsoft Cloud
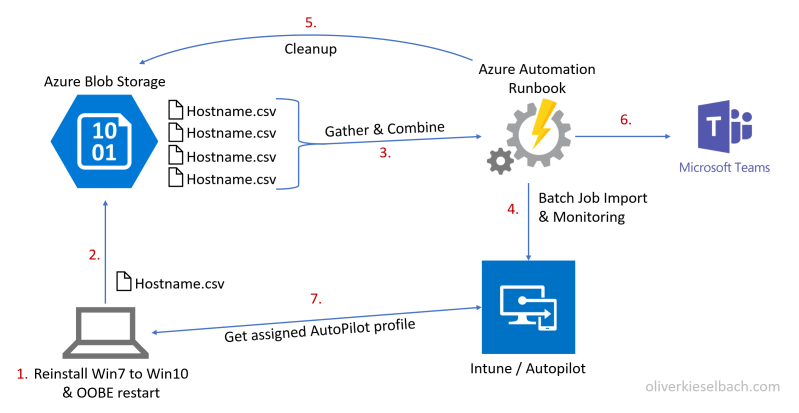
Complete process automation of gathering and upload of a device Autopilot information to the Windows Autopilot service with an Azure Automation Runbook.
Read MoreRecently I got the opportunity to join the team of awesome bloggers at SCConfigMgr.com. I’m really honored as the team is really great, in fact they are highly respected in the community 🙂 and it’s a real pleasure for me to join the team. I’ve written my first blog post there about WinPE and wireless support,…
Read MoreUPDATE 22/07/2018: New blog post Automation of gathering and importing Windows Autopilot information The Modern Management strategy is based on Enterprise Mobility + Security and additional services like Office 365. Microsoft created a new SKU called Microsoft 365 for this. To complete the big picture we need some additional services: Microsoft Store for Business Windows Analytics Windows…
Read More