Deploying BGInfo to quickly find your test devices or provide easy VM access during trainings with more visibility of the available user permissions.
Read More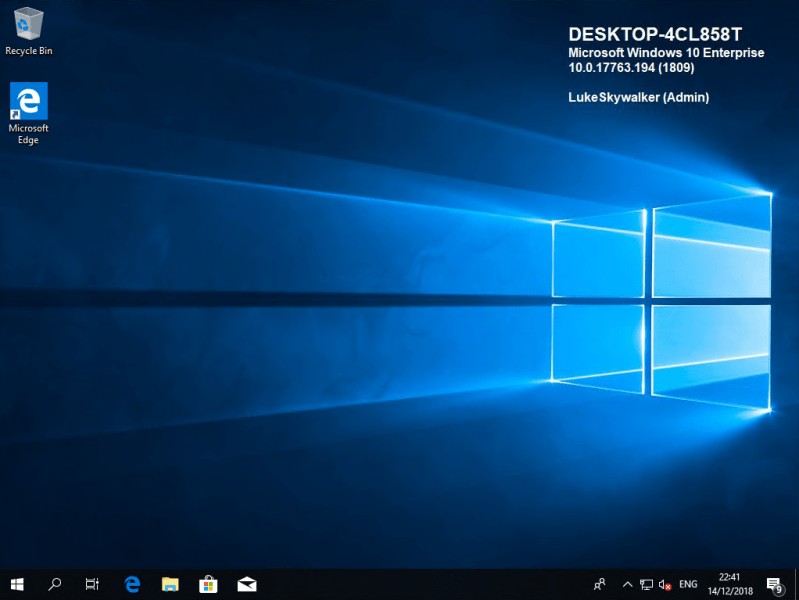
Enterprise Mobility and the Microsoft Cloud
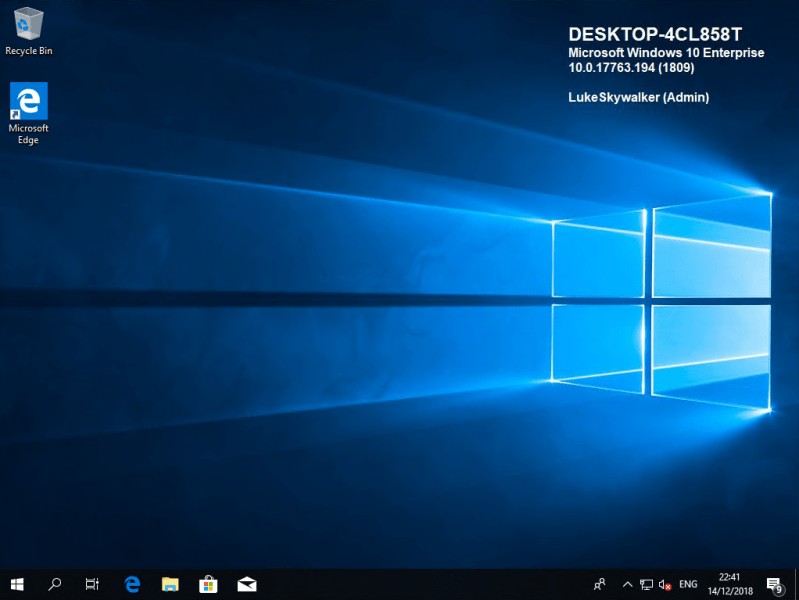
Deploying BGInfo to quickly find your test devices or provide easy VM access during trainings with more visibility of the available user permissions.
Read MoreThe Windows Defender Credential Guard is a feature to protect NTLM, Kerberos and Sign-on credentials. Windows 10 Enterprise provides the capability to isolate certain Operating System (OS) pieces via so called virtualization-based security (VBS). NTLM and Kerberos credentials are normally stored in the Local Security Authority (LSA). Once VBS is enabled the LSASS process will…
Read More